*Cube-Host– full cloud services!!
: Function WP_Styles::add was called incorrectly. The style with the handle "hello-elementor-child-style" was enqueued with dependencies that are not registered: hello-elementor-theme-style. Please see Debugging in WordPress for more information. (This message was added in version 6.9.1.) in /home/csrkub/domains/cube-vps.com/public_html/wp-includes/functions.php on line 6131
Notice: Function WP_Scripts::add was called incorrectly. The script with the handle "gpress-custom-js" was enqueued with dependencies that are not registered: gpress-siema. Please see Debugging in WordPress for more information. (This message was added in version 6.9.1.) in /home/csrkub/domains/cube-vps.com/public_html/wp-includes/functions.php on line 6131
*Cube-Host– full cloud services!!
Verification:
Removing from a group
Role group for the project/service
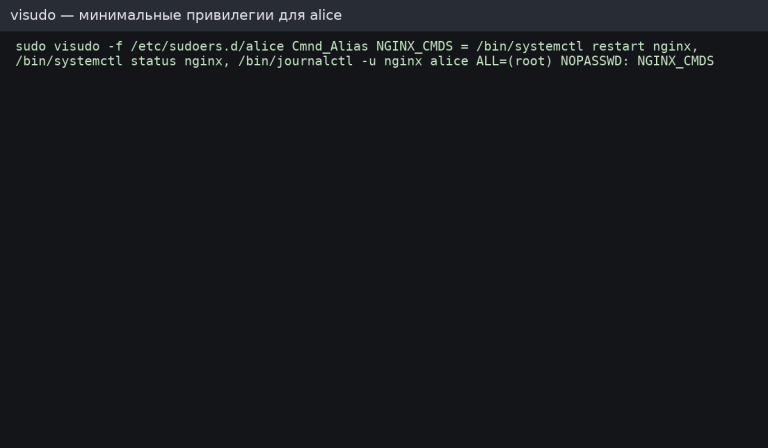
Edit rules only via visudo — validates syntax and saves you from the admin panel “brick.”
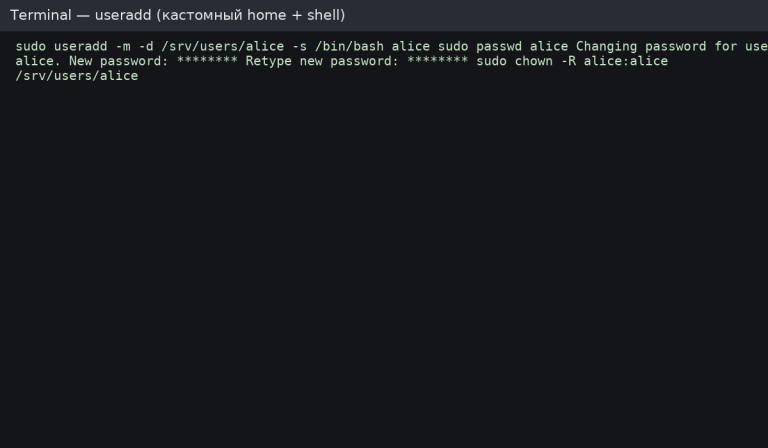
Full sudo (as in the sudo group):
Minimum privileges (example for nginx):
Tips
Install libpam-pwquality and configure /etc/pam.d/common-password, for example: