*Cube-Host– full cloud services!!
: Function WP_Styles::add was called incorrectly. The style with the handle "hello-elementor-child-style" was enqueued with dependencies that are not registered: hello-elementor-theme-style. Please see Debugging in WordPress for more information. (This message was added in version 6.9.1.) in /home/csrkub/domains/cube-vps.com/public_html/wp-includes/functions.php on line 6131
Notice: Function WP_Scripts::add was called incorrectly. The script with the handle "gpress-custom-js" was enqueued with dependencies that are not registered: gpress-siema. Please see Debugging in WordPress for more information. (This message was added in version 6.9.1.) in /home/csrkub/domains/cube-vps.com/public_html/wp-includes/functions.php on line 6131
*Cube-Host– full cloud services!!

We create a user and add them to sudo + the restrictive SSH group:
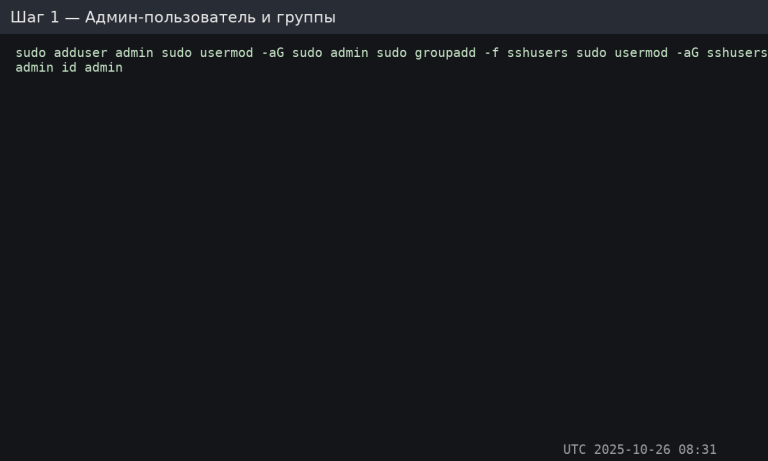
Locally (Windows/macOS/Linux):
On the server as root or an existing administrator:
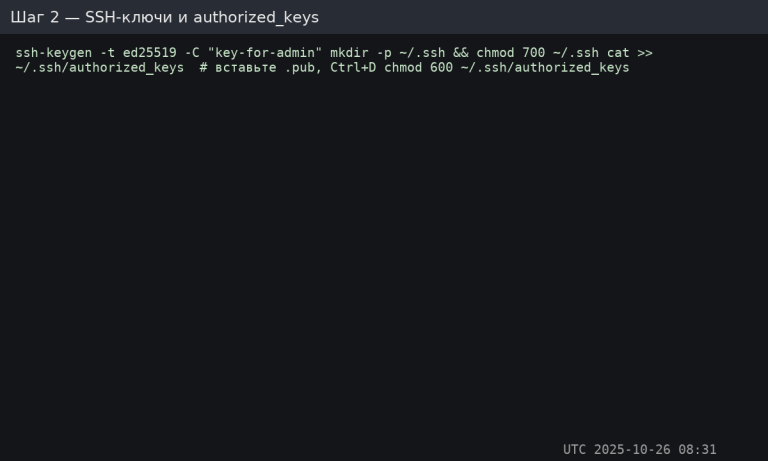
Important: only the public .pub key is sent to the server. The private key is stored locally.
Open /etc/ssh/sshd_config and specify:
Restart SSH:
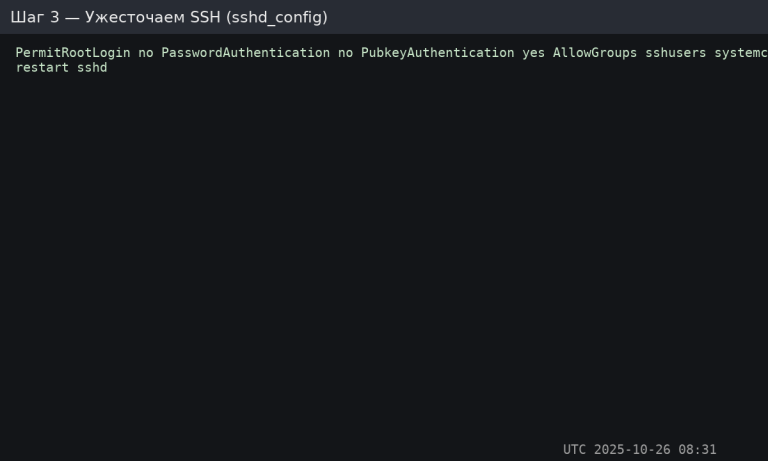
Verify that the keys work before disabling passwords, otherwise you will lose access.
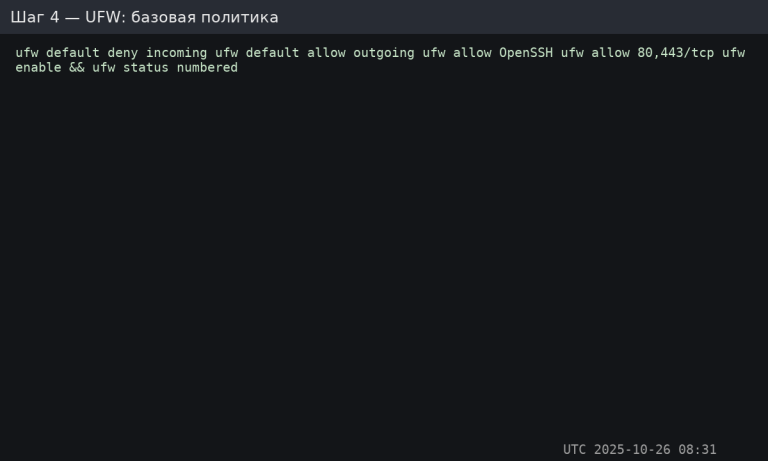
Need additional ports (e.g., 8080)? Add an explicit rule: sudo ufw allow 8080/tcp.
Create/edit
Restart:
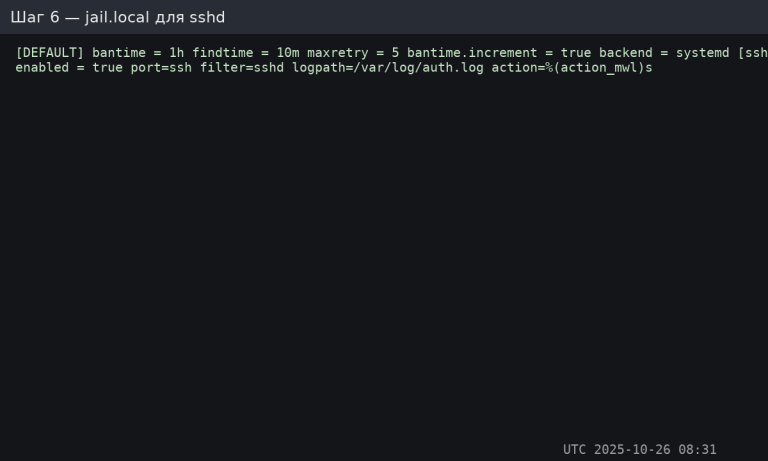
%(action_mwl)s will send an email (if email is configured) + log, and also block the IP.
Create a file
Apply:
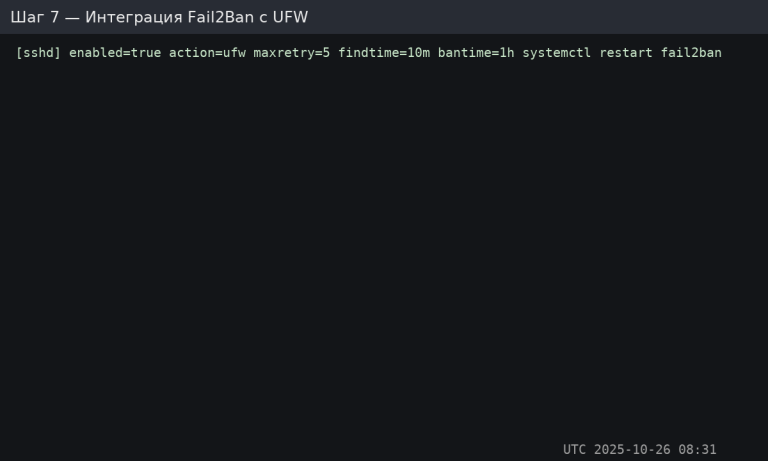
How to test the ban: from another node, make 5–6 incorrect login attempts, check the sshd status — the IP will appear in the list of blocked IPs.