*Cube-Host– full cloud services!!
: Function WP_Styles::add was called incorrectly. The style with the handle "hello-elementor-child-style" was enqueued with dependencies that are not registered: hello-elementor-theme-style. Please see Debugging in WordPress for more information. (This message was added in version 6.9.1.) in /home/csrkub/domains/cube-vps.com/public_html/wp-includes/functions.php on line 6131
Notice: Function WP_Scripts::add was called incorrectly. The script with the handle "gpress-custom-js" was enqueued with dependencies that are not registered: gpress-siema. Please see Debugging in WordPress for more information. (This message was added in version 6.9.1.) in /home/csrkub/domains/cube-vps.com/public_html/wp-includes/functions.php on line 6131
*Cube-Host– full cloud services!!


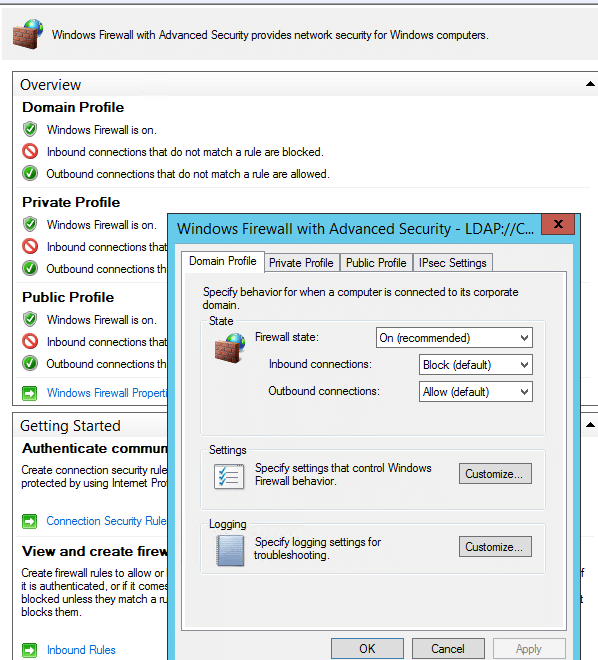
Windows Firewall has three profiles: Domain / Private / Public. On VPS, Public is usually active. Secure base — incoming: Block, outgoing: Allow.
GUI: “Windows Defender Firewall with Advanced Security” → root profile screen.
PowerShell:
Get-NetFirewallProfile | Select Name,Enabled,DefaultInboundAction,DefaultOutboundAction
Set-NetFirewallProfile -Profile Domain,Private,Public -Enabled True
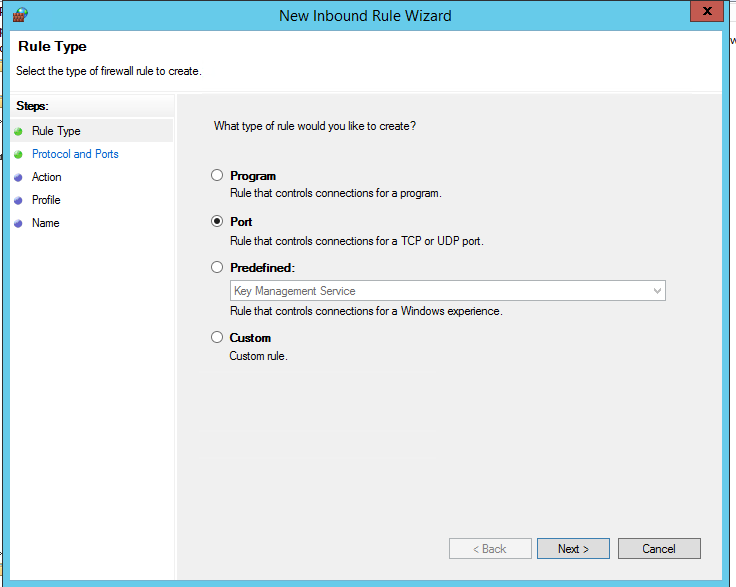
RDP is necessary for administering Windows VPS, but it cannot be opened to “everyone.” The procedure is straightforward: temporarily enable the default rules, create your own narrow rule based on the IP source, then disable the “broad” rules.
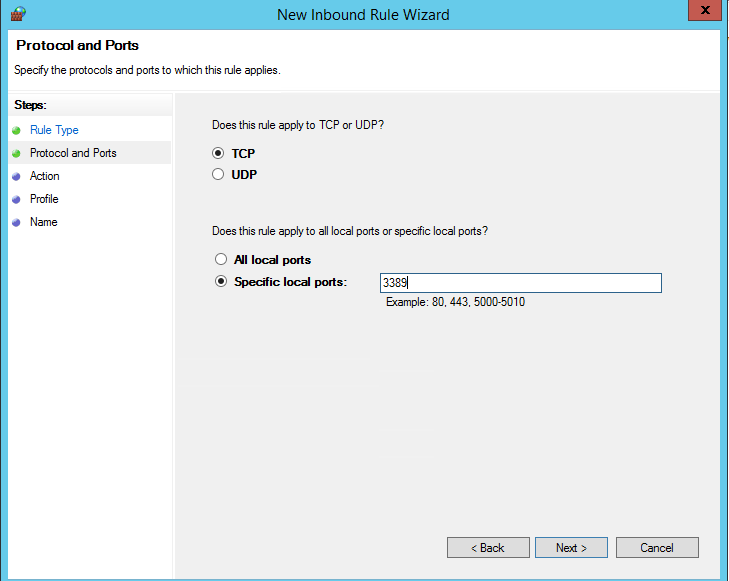
GUI (new rule wizard):
1. Inbound Rules → New Rule… → Port
2. TCP, Specific local ports: 3389
Allow the connection
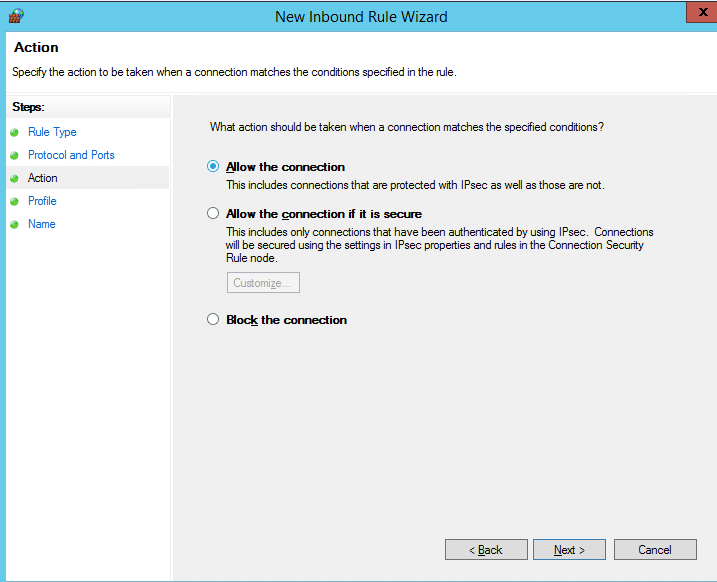
After creating it, go to Properties → Scope and specify Remote IP addresses (your static IP/VPN subnet). This is key to security.
PowerShell:
# When connecting for the first time: enable the standard group
Enable-NetFirewallRule -DisplayGroup "Remote Desktop"
# Strict rule only from your IP
New-NetFirewallRule -DisplayName "RDP inbound (admin IP only)" `
-Direction Inbound -Protocol TCP -LocalPort 3389 -Action Allow `
-RemoteAddress 203.0.113.50 -Profile Any
# After verification, disable “broad” RDP rules.
Disable-NetFirewallRule -DisplayGroup "Remote Desktop"
New-NetFirewallRule -DisplayName "HTTP (80)" -Direction Inbound -Protocol TCP -LocalPort 80 -Action Allow
New-NetFirewallRule -DisplayName "HTTPS (443)" -Direction Inbound -Protocol TCP -LocalPort 443 -Action Allow
New-NetFirewallRule -DisplayName "MSSQL (1433)" -Direction Inbound -Protocol TCP -LocalPort 1433 -Action Allow
(When accessing from restricted networks, set RemoteAddress for these rules as well.)
Record allowed and blocked connections in pfirewall.log.
GUI:
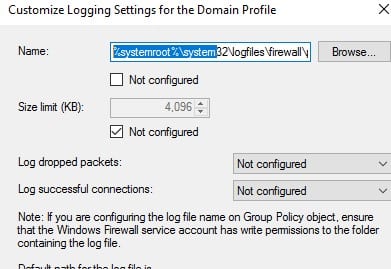
PowerShell:
Set-NetFirewallProfile -Profile Domain,Private,Public `
-LogFileName "C:WindowsSystem32LogFilesFirewallpfirewall.log" `
-LogMaxSizeKilobytes 32768 -LogAllowed True -LogBlocked True
From the client PC, verify that the necessary ports are accessible:
# RDP
Test-NetConnection vps.example.ru -Port 3389
# Веб
Test-NetConnection vps.example.ru -Port 80
Test-NetConnection vps.example.ru -Port 443
# SQL (if necessary)
Test-NetConnection vps.example.ru -Port 1433
TcpTestSucceeded: True — the rule works, the port is available. If False — check the rule profile, Scope (IP source), and external ACLs at the provider.